This is the fourth blog of a series analyzing the network traffic of Android RATs from our Android Mischief Dataset [more information here], a dataset of network traffic from Android phones infected with Remote Access Trojans (RAT). In this blog post we provide the analysis of the network traffic of the RAT05-AndroRAT [download here]. The previous blogs analyzed Android Tester RAT, DroidJack RAT, and SpyMax RAT.
Dissecting a RAT. Analysis of DroidJack v4.4 RAT network traffic.
This is the second blog of a series analyzing the network traffic of Android RATs from our Android Mischief Dataset, a dataset of network traffic from Android phones infected with Remote Access Trojans (RAT). In this blog post we provide the analysis of the network traffic of the RAT02-DroidJack v4.4.
Dissecting a RAT. Android Tester Trojan Analysis and Decoding.
This is the first blog post of a series analyzing the network traffic of Android RATs from our Android Mischief Dataset [more information here], a dataset of network traffic from Android phones infected with Remote Access Trojans (RAT). In this blog post we provide an analysis of the network traffic of the RAT01-Android Tester v6.4.6 [download here].
IoT-23 In Depth: CTU-IoT-Malware-Capture-1-1
This post is a continuation of the IoT-23 In Depth series based on the IoT-23 Dataset, the first dataset of malicious and benign IoT network traffic, that consists of 23 scenarios. In this blog post we provide an analysis of Scenario 9, CTU-IoT-Malware-Capture-60-1. This malware sample is called Hide-and-Seek. This variant is an IoT malware family capable of different types of DDoS attacks, exploits vulnerabilities in other devices, such as routers and wireless cameras, and to brute force the Telnet service across the Internet to expand its botnet. This malware makes use of the custom peer-to-peer (P2P) protocol to transfer data.
Writing a SLIPS Module
In this blogpost, we will walk through the process of developing a new SLIPS module: the VirusTotal (VT) module. This module will listen for new IP addresses and check them against VirusTotal API. VirusTotal returns detailed information on each IP, and the module will process this information and save it to the shared database.
Notes From The Lab: Sudden Increase of Traffic to Port 445
Today @VessOnSecurity tweeted that they have seen an increase on the number of SMB attacks in their honeypot (See Figure 1). We checked our telemetry and indeed we saw an increase on the incoming traffic to our honeypots on port 445. We will describe in this blog post the observations from our telemetry.
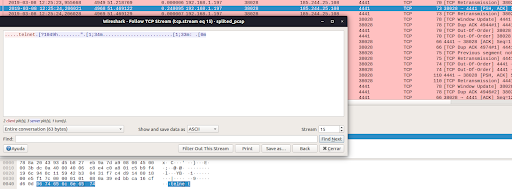
Hexa Payload Decoder Tool: A Tool To Automatically Extract and Decode Hex Data in C&C Servers
In this blog post we introduce the “Hexa Payload Decoder Tool”, a tool that is able to process a pcap file and return any decoded characters translated to English. This tool was developed to assist the network security analyst when working and interpreting data sent and received by command and control servers used by malware.